Guarding Your Digital Future: Technology Safety Best Practices Through the Years
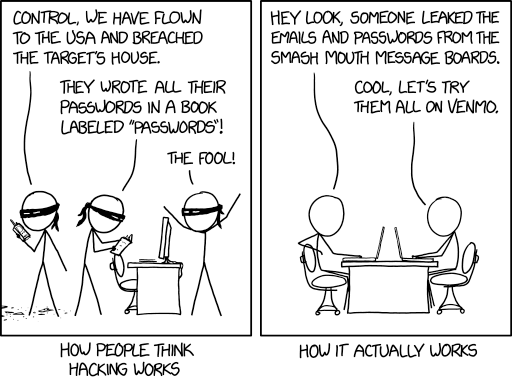
Remember when “cybersecurity” meant having a good antivirus program and maybe a firewall? Those days feel like ancient history now. As our digital world has evolved, so have the threats we face – and the practices we need to stay safe.
The Evolution of Digital Threats
The past few years have been eye-opening when it comes to cybersecurity. The WannaCry ransomware attack of 2017 [1] affected more than 200,000 computers across 150 countries, causing billions in damages. Just a month later, NotPetya [2] showed us how devastating a cyber attack could be to global business operations.
These weren’t just technical failures – they were wake-up calls that changed how we think about digital safety.
Core Safety Practices That Stand the Test of Time
1. Password Management Remember when “123456” was considered an acceptable password? (Shockingly, it’s still one of the most common passwords in 2019 [3]). Today’s best practices include:
- Using password managers to generate and store complex passwords
- Implementing multi-factor authentication wherever possible
- Regular password rotation for critical systems
- Never reusing passwords across different services
2. Data Protection Data breaches have become increasingly costly. The average cost of a data breach in 2019 is $3.92 million [4]. Essential protection measures include:
- Encrypting sensitive data both in transit and at rest
- Regular data backups following the 3-2-1 rule:
- 3 copies of your data
- 2 different types of storage media
- 1 copy stored off-site
- Clear data classification and handling procedures
- Regular security audits and penetration testing
3. Employee Training Your security is only as strong as your least security-aware employee. Modern training should cover:
- Phishing awareness and prevention
- Safe remote work practices
- Mobile device security
- Social engineering defense
- Incident reporting procedures
Emerging Best Practices
Cloud Security With more organizations moving to the cloud, new safety considerations have emerged:
- Implementing proper access controls and permissions
- Regular security configuration reviews
- Monitoring for unusual access patterns
- Data residency and compliance considerations
- Backup and disaster recovery planning
IoT Security The Internet of Things has introduced new vulnerabilities. Key considerations include:
- Segregating IoT devices on separate networks
- Regular firmware updates
- Strong default passwords
- Physical security measures
- Network monitoring for unusual behavior
Mobile Security With work increasingly happening on mobile devices, protection must extend beyond the office:
- Mobile Device Management (MDM) solutions
- App whitelisting and blacklisting
- Remote wipe capabilities
- Encrypted communications
- Regular security patches
Implementing a Modern Security Strategy
1. Risk Assessment Start by understanding your specific risks:
- Identify critical assets and systems
- Evaluate potential threats and vulnerabilities
- Assess potential impact of security breaches
- Prioritize security measures based on risk levels
2. Policy Development Create comprehensive but practical policies:
- Acceptable use guidelines
- Incident response procedures
- Data handling requirements
- Access control policies
- Remote work security guidelines
3. Technical Controls Implement appropriate security measures:
- Next-generation firewalls
- Endpoint protection solutions
- Email security gateways
- Web filtering
- Network monitoring tools
4. Regular Testing Verify your security measures through:
- Penetration testing
- Vulnerability scanning
- Phishing simulations
- Incident response drills
- Security awareness assessments
Looking Forward
As we move toward 2020, new challenges are emerging:
- AI-powered cyber attacks
- Quantum computing threats to encryption
- Advanced social engineering techniques
- Supply chain vulnerabilities
- State-sponsored cyber operations
Action Steps for Organizations
-
Assess Your Current State
- Conduct a security audit
- Review incident response plans
- Evaluate employee awareness levels
- Check compliance requirements
-
Plan Your Improvements
- Prioritize critical vulnerabilities
- Set realistic implementation timelines
- Allocate necessary resources
- Define success metrics
-
Implement and Monitor
- Roll out security measures systematically
- Train employees effectively
- Monitor for security events
- Measure effectiveness
Conclusion
Digital safety isn’t a destination – it’s a journey. The threat landscape continues to evolve, and our safety practices must evolve with it. The key is building a strong foundation of basic security practices while remaining flexible enough to adapt to new threats.
Remember: Security isn’t about being perfect; it’s about being prepared and vigilant. Start with the basics, build up your defenses systematically, and stay informed about emerging threats and best practices.